Bringing society the peace of mind we deserve
eEvidence is your digital trust services provider. Whether you communicate, notify, sign, create or share files, trust and legal certainty come by default - now and forever.
eEvidence is your digital trust services provider. Whether you communicate, notify, sign, create or share files, trust and legal certainty come by default - now and forever.

Signing a document is no longer a big deal. But when it comes to proving who signed what and when, most companies have a tough time.
Discover why businesses choose eEvidence’s when looking for the benefits of e-signatures plus an extra layer of legal certainty.

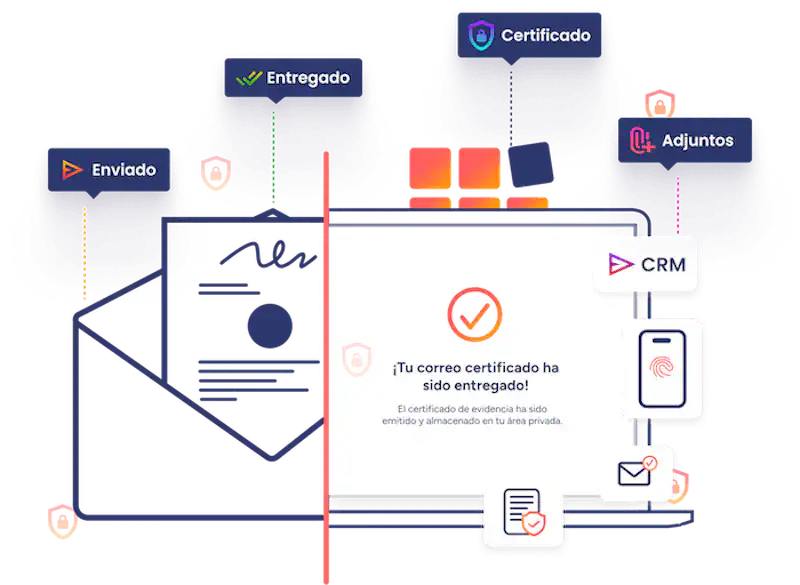
The leading electronic registered delivery service for reliable communications and notices with legally-binding proof of sending, delivery, content, and attachments.
Communicate and notify third parties with legally binding evidence.


The incorporation of eEvidence's digital solutions has allowed us to reinforce the legal security of electronic signature operations in the organization, as well as speed up the sending of registered communications.

As a pioneering university in online education, the UOC decided to start reinforcing the legal security of electronic communications exchanged with third parties from multiple departments.

eEvidence contributes to fulfilling our objective of digitizing the default recovery process for self-employed workers and SMEs in an efficient, scalable and optimized way. This is essential technology for Cobramus given the nature of our operations and the 100% digital business model.
Managed services are available to take the workload off your hands—simply prepare the data, set your preferences, and let our expert team handle the rest.

Secure identity verificación with KYC technology

Registered SMS for Secure Communication

API Integration for Seamless Access

Organizations around the world find security, reliability, and top-notch support with eEvidence. Wouldn’t you like to join?
